Key Skills for Cybersecurity Researcher Positions
Successful cybersecurity researcher professionals typically possess a combination of technical expertise, soft skills, and industry knowledge. Common skills include problem-solving abilities, attention to detail, communication skills, and proficiency in relevant tools and technologies specific to the role.
Typical Responsibilities
Cybersecurity Researcher roles often involve a range of responsibilities that may include project management, collaboration with cross-functional teams, meeting deadlines, maintaining quality standards, and contributing to organizational goals. Specific duties vary by company and seniority level.
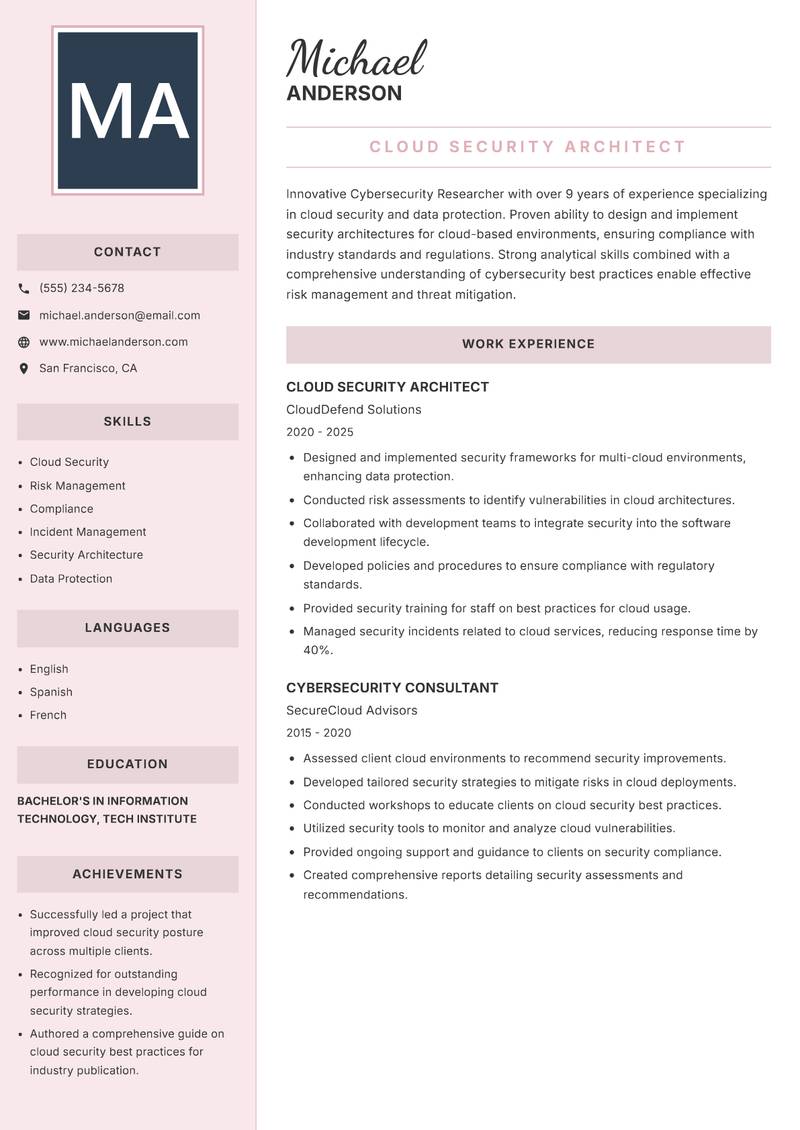
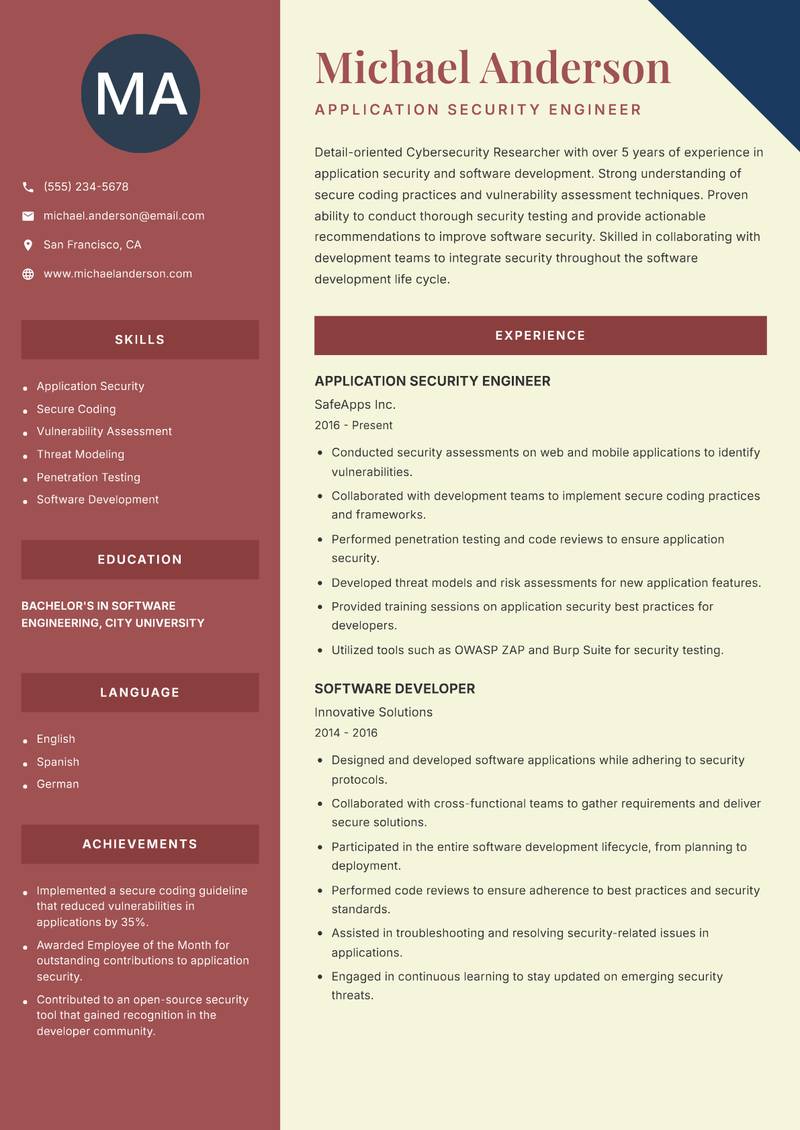
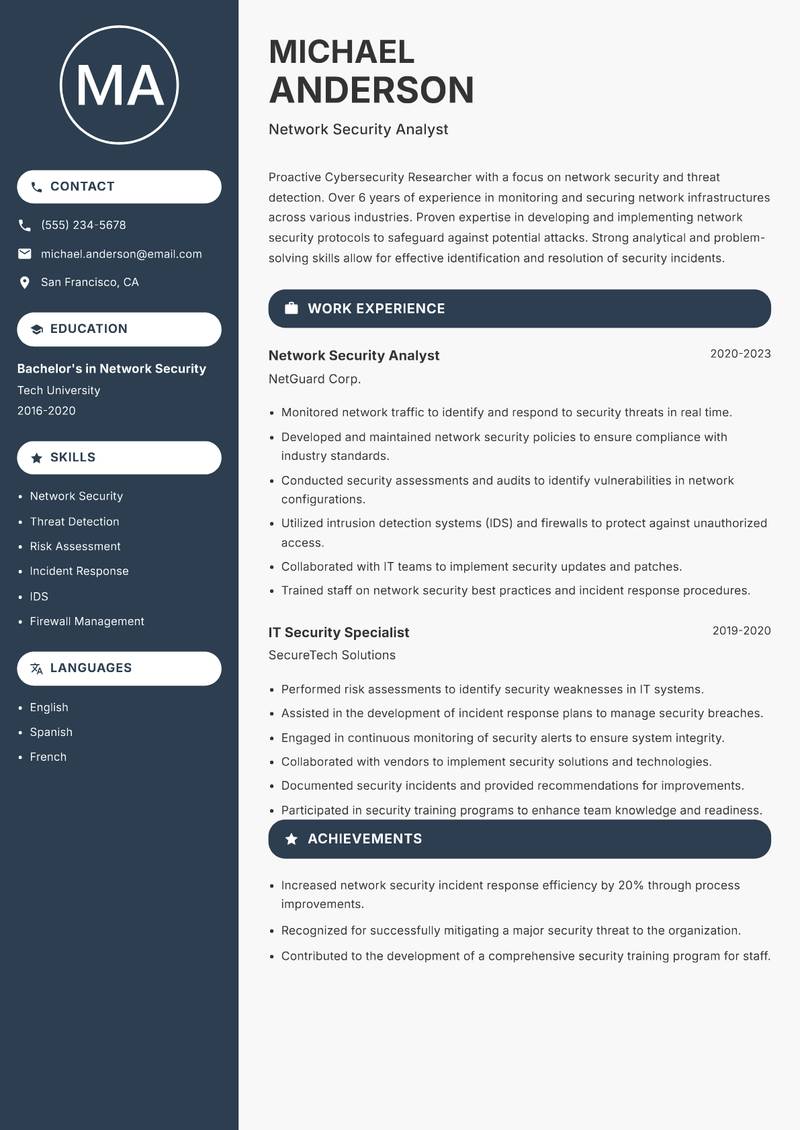
Resume Tips for Cybersecurity Researcher Applications
- Tailor your resume to match the job description keywords
- Highlight quantifiable achievements and metrics
- Use action verbs to describe your experience
- Keep your resume concise and focused (1-2 pages)
- Include relevant certifications and education
- Proofread carefully for grammar and spelling errors
ATS Optimization
Applicant Tracking Systems (ATS) scan resumes for keywords and formatting. To optimize your cybersecurity researcher resume for ATS:
- Use standard section headings (Experience, Education, Skills)
- Include relevant keywords from the job posting
- Avoid complex formatting, tables, or graphics
- Use standard fonts (Arial, Calibri, Times New Roman)
- Save as PDF or Word document format
- Ensure your contact information is clearly formatted